More than $15 billion worth of American cargo is lost to theft each year, making supply chain security a top concern for businesses nationwide. With cargo constantly shifting between warehouses, transport routes, and various partners, every transition exposes your goods to potential risk. Learning how to find weak points and prevent losses gives you a practical edge in keeping shipments safe, improving efficiency, and protecting your bottom line.
Table of Contents
- Step 1: Assess Vulnerabilities in Your Shipping Process
- Step 2: Implement Advanced Security Technologies
- Step 3: Train Staff on Theft Prevention Protocols
- Step 4: Strengthen Carrier and Partner Vetting
- Step 5: Monitor Shipments with Real-Time Tracking
- Step 6: Verify Security Measures and Review Performance
Quick Summary
| Key Point | Explanation |
|---|---|
| 1. Identify Vulnerabilities in Your Shipping Process | Map out your logistics to find weak points that could lead to cargo theft and create targeted risk mitigation strategies. |
| 2. Implement Advanced Security Technologies | Use modern tracking systems and tamper-evident seals to protect your shipments and provide immediate alerts against unauthorized access. |
| 3. Train Staff on Theft Prevention Protocols | Educate employees on recognizing suspicious activities and proper response techniques to enhance your first line of defense against theft. |
| 4. Strengthen Carrier and Partner Vetting | Conduct thorough background checks on carriers and logistics partners to minimize vulnerabilities and ensure high security standards. |
| 5. Monitor Shipments with Real-Time Tracking | Utilize GPS and geo-fencing to maintain continuous visibility over your shipments, enabling quick responses to potential threats. |
Step 1: Assess Vulnerabilities in Your Shipping Process
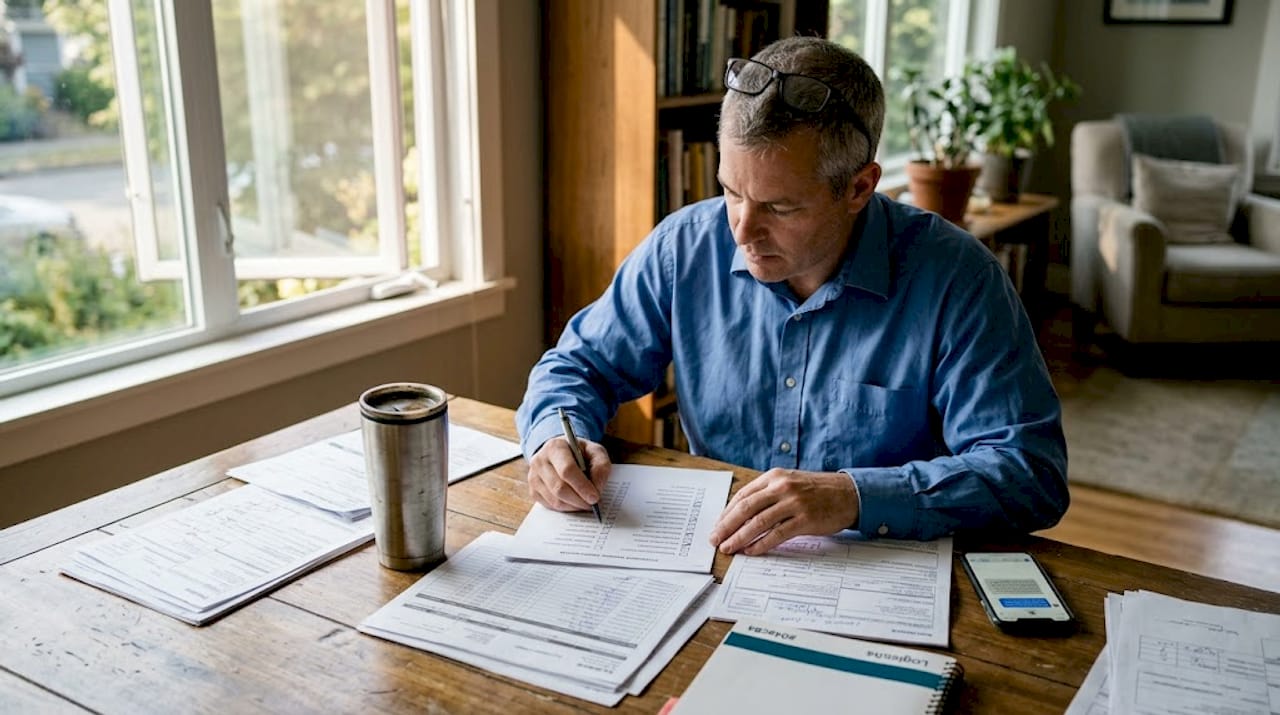
Securing your supply chain starts with identifying potential weak points that could expose your cargo to theft. The assessment process requires a systematic approach that examines every stage of your shipping workflow, from warehouse storage to final delivery. Understanding your vulnerabilities allows you to create targeted strategies that minimize risk and protect your valuable inventory.
To effectively assess shipping vulnerabilities, start by mapping out your entire logistics process and analyzing each transition point where cargo might be exposed. Focus on conducting a comprehensive supply chain risk management review that evaluates potential entry points for theft. This means examining your warehouse security protocols, transportation routes, loading procedures, and handoff points between different logistics partners. Pay special attention to high-risk zones such as truck parking areas, shipping docks, and transfer stations where cargo is most likely to be targeted.
Pro tip: Document each vulnerability you discover with specific details about potential risks, including estimated probability and potential financial impact. This granular approach will help you prioritize your security investments and develop a targeted risk mitigation strategy. By treating cargo theft prevention as an ongoing process of assessment and improvement, you can stay one step ahead of potential criminal activities and protect your business’s bottom line.
Step 2: Implement Advanced Security Technologies
Protecting your cargo requires more than traditional security measures. Modern supply chain security demands cutting-edge technological solutions that can actively monitor and prevent potential theft or damage. By strategically integrating advanced security technologies, you can create multiple layers of protection that dramatically reduce your vulnerabilities.
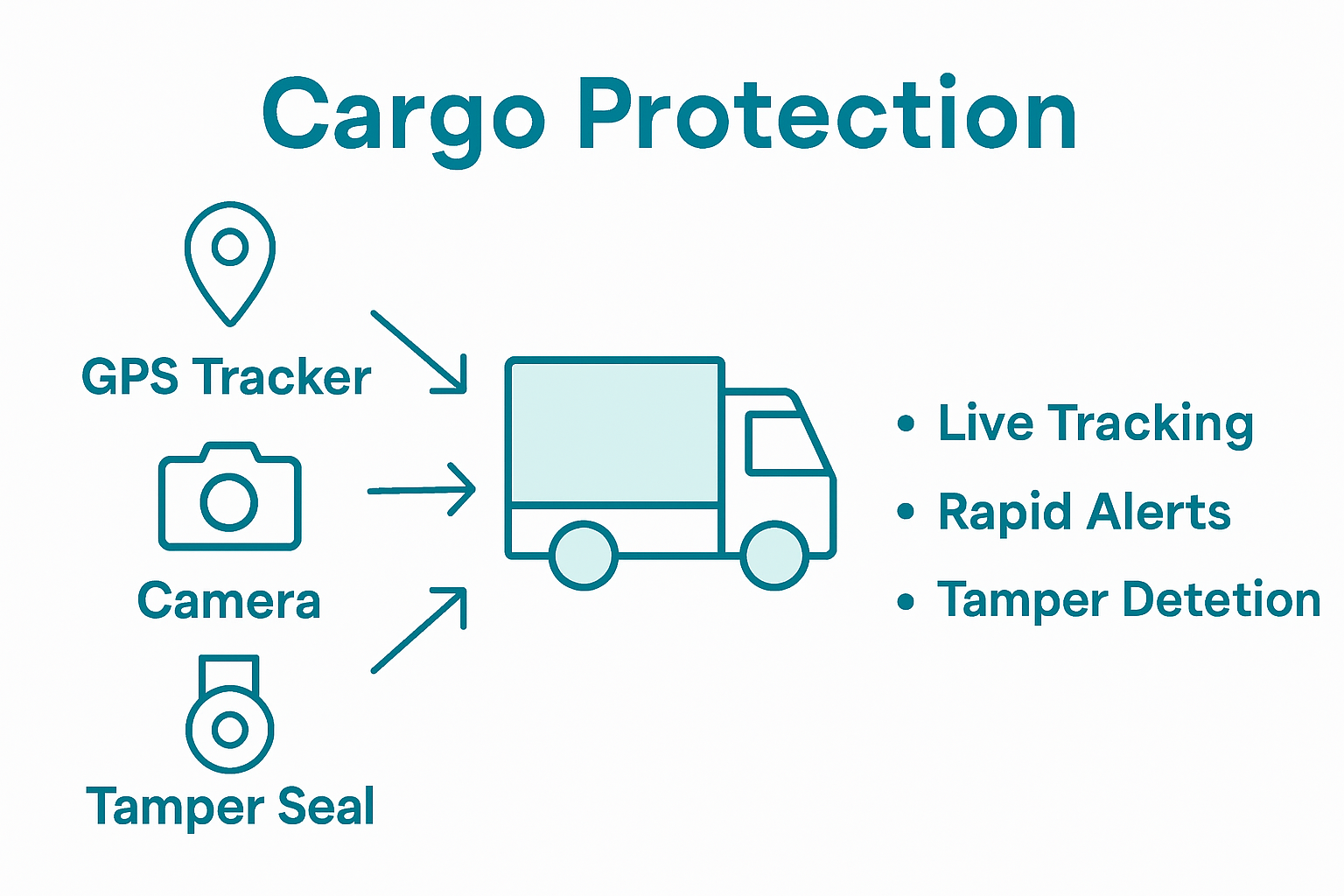
Start by exploring comprehensive tracking and monitoring systems that provide real-time visibility into your shipments. Cargo fire detection technologies represent an excellent example of innovative security solutions that can prevent significant losses. Consider implementing GPS tracking devices, wireless sensor networks, and tamper-evident seals that can instantly alert you to unauthorized access or unexpected route deviations. These technologies not only help prevent theft but also provide critical documentation if an incident occurs.
Pro tip: When selecting security technologies, prioritize solutions that integrate seamlessly with your existing logistics infrastructure. Look for systems that offer comprehensive reporting, immediate alerts, and compatibility with your current tracking and management platforms. Remember that technology is most effective when it becomes an intuitive part of your overall security strategy rather than a standalone solution. By continuously evaluating and upgrading your technological defenses, you can stay ahead of emerging threats and protect your valuable cargo more effectively.
Step 3: Train Staff on Theft Prevention Protocols
Protecting your supply chain requires more than technological solutions strategic employee education plays a crucial role in preventing cargo theft. Your staff represents the first line of defense against potential security breaches, making comprehensive training an essential component of your overall risk management strategy.

Implements a robust cargo security program that covers multiple critical areas of prevention. Focus on developing training modules that teach employees how to recognize suspicious activities, understand proper documentation procedures, and respond effectively to potential security threats. This training should include practical skills such as conducting thorough vehicle inspections, identifying potential security risks during transportation, and understanding the precise protocols for reporting and responding to suspicious incidents.
Pro tip: Create a culture of security awareness that goes beyond standard training sessions. Develop ongoing education programs that regularly update staff on new theft tactics, reinforce existing protocols, and encourage a proactive approach to cargo protection. By transforming security from a compliance requirement to a shared organizational responsibility, you empower your team to become active guardians of your supply chain integrity.
Step 4: Strengthen Carrier and Partner Vetting
Building a secure supply chain begins with carefully selecting and thoroughly screening your transportation partners. Your carrier network represents a critical vulnerability point that requires meticulous evaluation to prevent potential cargo theft risks. By implementing rigorous vetting processes, you can significantly reduce the likelihood of security breaches and protect your valuable shipments.
Comprehensive background screening is essential when evaluating potential carriers and logistics partners. Develop a systematic approach that goes beyond basic documentation checks and includes in depth investigations of company histories, safety records, and operational practices. This means conducting thorough background checks on key personnel, verifying company credentials, examining their security protocols, and ensuring they demonstrate a commitment to maintaining high security standards. Carrier vetting strategies should include analyzing past performance records, checking insurance coverage, and confirming compliance with industry safety regulations.
Pro tip: Create a dynamic vetting scorecard that continually evaluates your partners performance. Do not treat carrier screening as a one time process but as an ongoing assessment that requires regular review and updates. By maintaining a proactive approach to partner evaluation, you can quickly identify and address potential security vulnerabilities before they become significant risks to your supply chain integrity.
Step 5: Monitor Shipments with Real-Time Tracking
Effective cargo protection demands continuous visibility into your shipment’s location and status. Real-time tracking transforms your ability to prevent theft by providing instant insights into your cargo’s movement, enabling rapid response to any potential security threats. This technological approach allows you to stay one step ahead of potential criminals and maintain complete control over your supply chain.
Advanced tracking technologies enable comprehensive shipment monitoring through sophisticated GPS and geo-fencing solutions. Implement a multi-layered tracking strategy that includes covert GPS trackers, wireless sensor networks, and real-time monitoring platforms. These systems should provide immediate alerts for unauthorized route deviations, unexpected stops, or potential security breaches. International parcel shipping becomes significantly more secure when you can pinpoint your cargo’s exact location at any moment, reducing the window of vulnerability for potential theft.
Pro tip: Configure your tracking system to create automated notification protocols that immediately alert your security team about any suspicious activity. Develop clear response procedures that define exactly how your team will react to different types of tracking alerts. Remember that real-time monitoring is not just about collecting data but about creating a proactive security ecosystem that can respond instantly to potential threats.
Step 6: Verify Security Measures and Review Performance
Effective cargo theft prevention requires ongoing assessment and continuous improvement of your security strategies. Regularly evaluating your existing protective measures helps identify potential vulnerabilities and ensures your approach remains adaptive and robust against emerging threats. This systematic review process is crucial for maintaining the integrity of your supply chain security protocols.
Comprehensive security audits are essential for uncovering potential gaps in your protective infrastructure. Develop a structured review process that integrates multiple layers of analysis, including technology effectiveness, procedural compliance, and physical security performance. Layered security strategies demand continuous evaluation of your process and technology integration, ensuring that each component of your security ecosystem works seamlessly together to prevent potential theft incidents.
Pro tip: Create a performance scorecard that tracks key security metrics such as incident rates, response times, and vulnerability identification. Establish a quarterly review process where your security team conducts a deep dive into these metrics, comparing current performance against previous benchmarks and industry standards. This data-driven approach transforms security from a reactive measure to a proactive, continuously improving system that anticipates and neutralizes potential threats before they can impact your supply chain.
Strengthen Your Supply Chain Security with Trusted Logistics Solutions
Cargo theft threatens your business by exposing vulnerabilities in shipping, carrier vetting, and real-time tracking. This creates costly disruptions and puts your valuable inventory at risk. To effectively combat these challenges, you need reliable courier services combined with advanced tools that ensure end-to-end shipment visibility and proactive theft prevention.
Take control by partnering with Or-Ner, a comprehensive platform tailored for ecommerce sellers and global brands. From secure freight booking to real-time shipment tracking and dedicated warehousing, Or-Ner integrates multiple layers of protection discussed in the article such as risk management, technology integration, and carrier evaluation. Don’t wait until theft happens. Explore how Or-Ner’s reliable courier services and cross-border logistics can safeguard your supply chain and ensure seamless delivery. Protect your business today by visiting Or-Ner and discovering solutions that keep your cargo secure and your operations moving forward.
Frequently Asked Questions
How can I assess vulnerabilities in my shipping process to prevent cargo theft?
To assess vulnerabilities, start by mapping your entire logistics process and analyzing each transition point where cargo may be exposed. Document vulnerabilities with details about potential risks and their financial impact to prioritize your security investments.
What advanced security technologies should I implement to secure my supply chain?
Implement technologies such as GPS tracking devices, wireless sensor networks, and tamper-evident seals. These solutions can alert you to unauthorized access or unexpected route deviations, enhancing your cargo protection significantly.
What training should I provide to my staff regarding theft prevention protocols?
Create a comprehensive cargo security training program that teaches employees how to recognize suspicious activities and respond effectively. Include practical skills such as conducting vehicle inspections and understanding reporting protocols to empower your team as your first line of defense.
How do I verify the security measures of my logistics partners?
Conduct comprehensive background screenings of your transportation partners, focusing on their safety records and security practices. Use a dynamic vetting scorecard to regularly assess their performance and ensure they maintain high security standards.
What steps can I take to monitor shipments in real time?
Implement advanced tracking technologies, including covert GPS trackers and real-time monitoring platforms. Configure your system to provide immediate alerts for any unauthorized deviations to maintain continuous visibility and control over your shipments.
How often should I review my security measures and performance?
Regularly perform comprehensive security audits to identify potential vulnerabilities and gaps in your protective measures. Establish a quarterly review process to analyze key security metrics, allowing you to adapt and improve your strategies continuously.
Recommended
- Top Benefits of Freight Forwarding for Growing Businesses 2025 – ORNER
- What Is Freight Forwarding? Guide for Modern Supply Chains 2025 – ORNER
- Just in Time Delivery: Essential Guide for 2025 Success – ORNER
- Essential courier services for small businesses – ORNER
- Essential Guide to Preparing for International Shipping 2025 | Schott Removals
- Understanding Cannabis Product Shipping Laws: What You Need to Know – California Blendz