Cargo theft has surged into a leading supply chain concern for many American ecommerce companies, with experts estimating losses reach billions each year. This relentless threat challenges even seasoned logistics managers, who must guard against both physical and digital attacks that disrupt reliable delivery. Gaining a clear understanding of what cargo theft truly means is the first step toward building stronger defenses that protect shipments, profits, and reputation across the complex American logistics network.
Table of Contents
- Defining Cargo Theft In Logistics
- Types And Methods Of Cargo Theft
- Technology Solutions For Theft Prevention
- Legal Responsibilities And Compliance Measures
- Common Vulnerabilities And How To Avoid Them
Key Takeaways
| Point | Details |
|---|---|
| Understanding Cargo Theft | Cargo theft is a multifaceted issue, merging physical and digital theft methods that pose significant risks to logistics operations. |
| Implement Technology Solutions | Utilizing advanced tracking systems and cybersecurity protocols can enhance the protection of shipments against theft. |
| Compliance with Legal Standards | Adhering to federal regulations and security frameworks is crucial for mitigating risks and protecting supply chains. |
| Identify Vulnerabilities | Regular vulnerability assessments are essential in uncovering potential threats within both technological systems and human processes. |
Defining Cargo Theft in Logistics
Cargo theft represents a complex and evolving challenge for logistics professionals, encompassing unauthorized removal of shipments across multiple points in the supply chain. At its core, cargo theft involves the deliberate stealing of goods during transportation, storage, or delivery processes, with significant financial implications for businesses.
The landscape of cargo theft has transformed dramatically, expanding beyond traditional physical theft to include sophisticated cyber intrusions. Contemporary cargo theft strategies now integrate both physical and digital approaches, making security increasingly complex for ecommerce logistics managers. Criminals may target shipments through opportunistic street-level theft or organize elaborate schemes involving insider information and technological manipulation.
Understanding cargo theft requires recognizing its multifaceted nature. Package theft can occur at multiple supply chain stages, including warehouses, transportation routes, and final delivery points. Estimates suggest cargo theft costs United States businesses billions of dollars annually, with some incidents remaining unresolved. Common methods include truck hijackings, warehouse break-ins, identity theft of carrier credentials, and emerging digital infiltration techniques that compromise operational systems.
Pro tip: Implement a comprehensive cargo tracking system with real-time geolocation monitoring to quickly identify and respond to potential theft attempts.
Types and Methods of Cargo Theft
Cargo theft encompasses a sophisticated range of methods that target shipments through strategic and opportunistic approaches. Theft strategies span multiple supply chain points, from initial warehouse storage to final delivery locations, presenting significant challenges for logistics professionals.
Primary cargo theft methods can be categorized into several distinct types. Opportunistic theft involves individual actors targeting easily accessible shipments, such as porch piracy where packages are stolen directly from residential delivery points. Organized crime theft represents a more complex approach, involving coordinated teams that may use advanced techniques like tracking delivery vehicles, creating fake shipping credentials, or infiltrating logistics operations.

Legal frameworks in the United States recognize multiple cargo theft techniques, including truck hijacking, warehouse break-ins, and sophisticated digital infiltration. Advanced theft methods now incorporate technological components like GPS tracking of valuable shipments, intercepting delivery routes, and using insider information to target high-value cargo. Common tactics also include partial load theft (pilferage), where criminals strategically remove only portions of shipment contents and replace them with weights to maintain package integrity.
Here’s a summary of major cargo theft methods and their impacts:
| Theft Method | Typical Target Location | Complexity Level | Business Impact |
|---|---|---|---|
| Opportunistic Theft | Residential/Delivery Points | Low | Small losses, customer claims |
| Organized Crime | Warehouses, Truck Routes | High | Large losses, reputation risk |
| Identity/Tech Manipulation | Logistics Systems | Very High | Fraud, data breach exposure |
| Partial Load Pilferage | Warehouses, Transit Routes | Medium | Undetected shrinkage, liability |
Pro tip: Develop a multi-layered security protocol that combines physical tracking, digital monitoring, and periodic supply chain vulnerability assessments to proactively identify and mitigate potential theft risks.
Technology Solutions for Theft Prevention
Advanced technology solutions are transforming cargo theft prevention, offering logistics managers sophisticated tools to secure shipments across complex supply chains. Emerging cybersecurity trends demonstrate the integration of physical and digital security approaches, creating comprehensive protection strategies that go beyond traditional security methods.
Key technological interventions include AI-powered tracking systems, real-time geolocation monitoring, and advanced predictive analytics. These technologies enable logistics professionals to implement proactive security measures, tracking shipments with unprecedented precision. GPS tracking devices, tamper-evident seals, and blockchain-based verification systems have become critical components in modern cargo protection strategies, providing instantaneous insights into shipment status and potential vulnerabilities.
Government-supported security partnerships like the Customs Trade Partnership Against Terrorism (CTPAT) offer additional technological frameworks for enhancing supply chain security. These programs provide guidelines for implementing cutting-edge cybersecurity protocols, including advanced encryption techniques, threat intelligence sharing platforms, and comprehensive vulnerability assessment tools. Modern technology solutions now integrate machine learning algorithms that can predict potential theft risks by analyzing historical data, route patterns, and emerging criminal strategies.
Pro tip: Invest in integrated security technology that combines real-time tracking, AI-driven anomaly detection, and comprehensive threat intelligence to create a multi-layered cargo protection ecosystem.
The table below compares popular technology solutions for cargo theft prevention:
| Technology Solution | Main Function | Notable Advantage | Limitation |
|---|---|---|---|
| GPS Tracking Devices | Real-time location monitoring | Immediate alerts | Signal interference risks |
| Tamper-Evident Seals | Detect unauthorized access | Visual deterrence | Can be physically bypassed |
| Blockchain Verification | Secure shipment authentication | Immutable records | High deployment costs |
| Predictive Analytics | Risk analysis using data patterns | Proactive threat response | Requires large data sets |
Legal Responsibilities and Compliance Measures
Cargo theft prevention involves a complex network of legal responsibilities that extend far beyond simple operational protocols. Federal legislation establishes comprehensive security frameworks designed to protect supply chains from potential threats, requiring logistics companies to implement rigorous risk management strategies and comprehensive security protocols.
The legal landscape for cargo protection encompasses multiple regulatory requirements that mandate proactive security measures. Compliance standards now require businesses to develop detailed security plans, conduct thorough personnel vetting, and maintain robust information technology safeguards. Key legal obligations include maintaining detailed documentation of shipment processes, implementing strict access control mechanisms, and establishing transparent reporting protocols for potential security breaches.
Government partnerships like the Customs Trade Partnership Against Terrorism (CTPAT) provide structured frameworks for companies to demonstrate their commitment to supply chain security. These programs offer incentives such as reduced inspection frequencies for companies that meet stringent security standards, creating a collaborative approach between private sector logistics providers and federal regulatory agencies. Companies participating in such programs must develop comprehensive threat assessment strategies, maintain continuous employee training, and implement advanced cybersecurity protocols.
Pro tip: Develop a dedicated compliance team that regularly reviews and updates your cargo security protocols to ensure alignment with the latest federal security requirements and industry best practices.
Common Vulnerabilities and How to Avoid Them
Comprehensive supply chain security requires understanding critical vulnerabilities that can compromise logistics operations. Ecommerce logistics managers must recognize the intricate ways potential threats can infiltrate shipping processes, ranging from technological weaknesses to human error and systemic operational gaps.
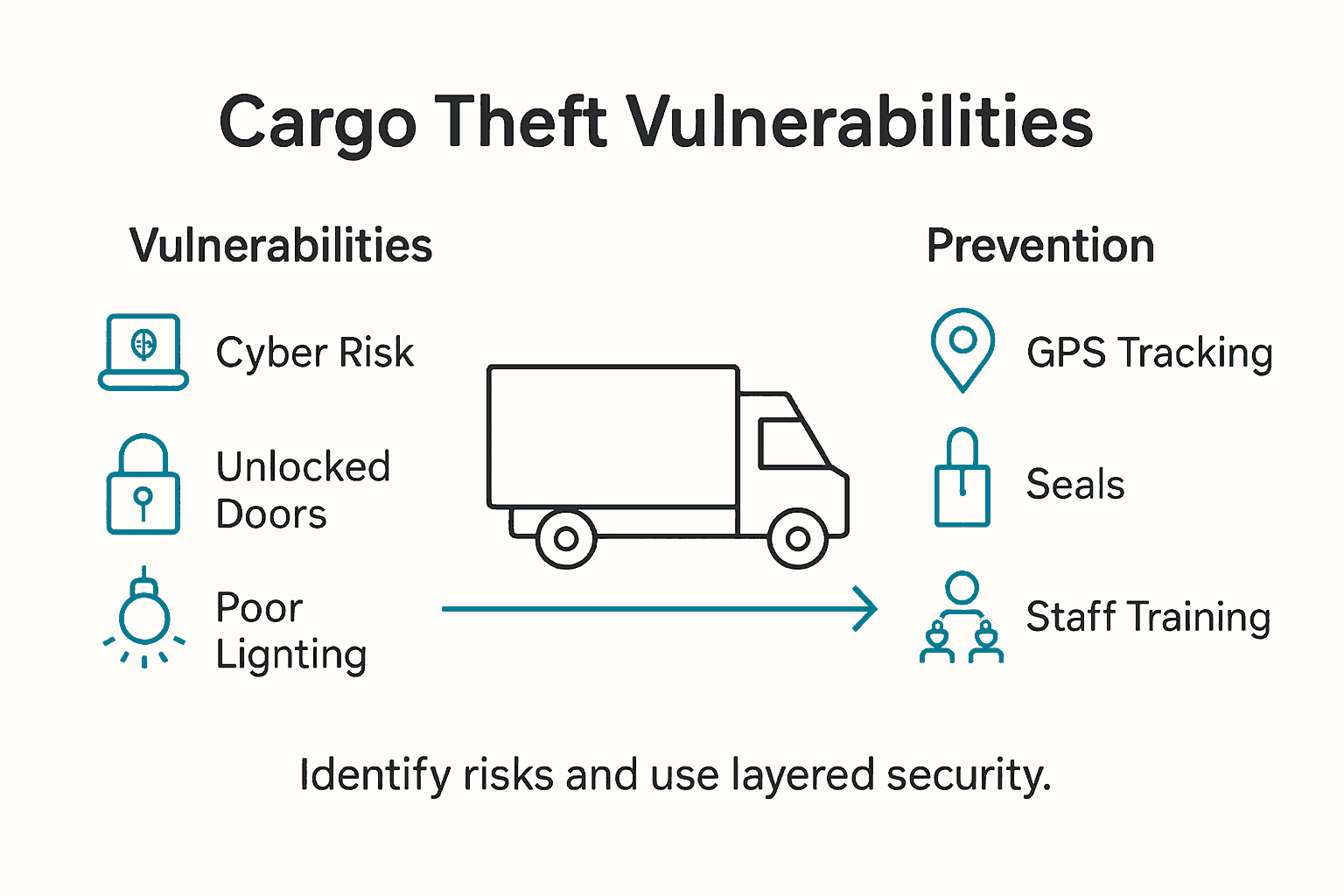
Cybersecurity vulnerabilities represent a significant risk landscape for modern shipping operations. Emerging cybersecurity trends reveal multiple potential attack vectors, including sophisticated social engineering techniques, identity compromise, and technological system infiltrations. Common weak points include unsecured communication channels, inadequate employee training, outdated software systems, and insufficient authentication protocols that can be exploited by sophisticated criminal networks.
Physical infrastructure vulnerabilities complement digital risks, creating complex challenges for logistics security professionals. Key exposure points include unsecured loading facilities, insufficient vehicle tracking mechanisms, limited package screening processes, and gaps in personnel credentialing. Critical mitigation strategies involve implementing comprehensive security layers that address both technological and human elements, including advanced tracking technologies, robust employee screening processes, continuous security awareness training, and real-time threat intelligence monitoring.
Pro tip: Conduct quarterly comprehensive vulnerability assessments that systematically evaluate both technological systems and human processes to identify and address potential security gaps before they can be exploited.
Protect Your Ecommerce Shipments with Reliable Courier Services from Or-Ner
Cargo theft poses a growing threat to ecommerce sellers across the United States. As the article highlights, security breaches can occur at every stage of the supply chain—from warehouse pilferage to identity theft and cyberattacks on logistics systems. These vulnerabilities can cause significant financial loss, operational disruptions, and damage to your brand’s reputation. The challenge is clear: to safeguard shipments through real-time tracking, multi-layered security protocols, and compliance with federal regulations.
Choose reliable courier services that provide end-to-end visibility and advanced security solutions tailored for ecommerce businesses. Or-Ner offers a comprehensive platform integrating real-time shipment tracking, customs clearance, and scalable warehousing options to protect your cargo against evolving theft methods. Managing inventory, cross-border logistics, and fulfillment has never been easier or more secure. Take control of your supply chain risks today and experience peace of mind by partnering with Or-Ner. Visit our homepage now to strengthen your logistics backbone and safeguard your shipments from start to finish.
Frequently Asked Questions
What are the common methods of cargo theft in logistics?
Cargo theft can occur through various methods, including opportunistic theft like porch piracy, organized crime theft involving sophisticated techniques, and partial load pilferage where only parts of shipments are stolen. These methods target different points in the supply chain, like warehouses and delivery locations.
How can technology help prevent cargo theft?
Advanced technology solutions such as GPS tracking devices, tamper-evident seals, and blockchain verification systems can significantly enhance cargo theft prevention. These tools provide real-time monitoring, secure authentication of shipments, and help logistics professionals respond proactively to potential theft risks.
What legal obligations do companies have for cargo security?
Companies are required to develop detailed security plans, maintain comprehensive documentation, and implement strict access control measures. Compliance with federal security frameworks, like CTPAT, lays out additional guidelines for security protocols and risk management in logistics operations.
How can businesses identify and mitigate vulnerabilities in their shipping processes?
Businesses can identify vulnerabilities by conducting comprehensive security assessments that encompass both technological weaknesses and human errors. This includes ensuring secure communication channels, updating software systems, and implementing robust employee training programs to address potential threats.